It’s Everybody
Smart computer users protect their PCs from hacks. They know that there are countless ways that a hacker can take advantage of a PC. If individuals know they are at risk, how can any business think that they are too small to worry?
Yes, Even You!
Any business owner who thinks that they’re impervious is in for a rude awakening. The smart business owner realizes that hackers have found ways to monetize just about any data that can be found on a computer. It’s a matter of time before your business gets hit.
Your Computer as a Spambot?
Any PC can be a goldmine for hackers. Hackers can turn your PC into a spambot, infecting it with spyware and trojans to collect information from every one of your contacts. Using your computer, they can spread threats through a botnet.
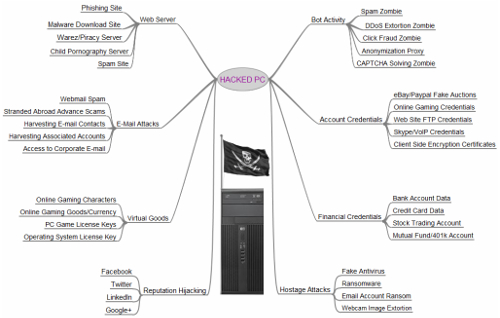
To emphasize just how dangerous an infected PC can be, check out this infographic used by Brian Krebs on his security website:
It’ll Cost You
As you can see, hackers have no shortage of possibilities with the average user’s PC. No matter what your PC or workstation is being used for, a hacker can access whatever credentials or personal information is on it. The average cost of a data breach per lost or stolen record is $154, so even if you only have a few hundred contact records, it’s going to hurt.
Obviously, you should be taking advantage of proactive security solutions designed to minimize risk, so your organization can catch small issues and resolve them before they become difficult to contain.
Cybersecurity Countermeasures
Enter the Unified Threat Management (UTM) solution; a great tool that can help any business avoid the majority of threats to your IT infrastructure. The UTM uses powerful security tools like enterprise-level firewalls and antiviruses, and compounds them with preventative tools like web content filtering and spam blocking.
With the UTM solution, your business can dodge the majority of threats thrown your way. No, there is no guarantee that you’ll never be targeted, so it’s your responsibility to stay vigilant, train your people, and mitigate potential damage before it happens.
Trusted Help
Quikteks knows cybersecurity. Our trusted technicians can help to pinpoint weak links in your system infrastructure. We can show you how to remedy them with best practices and security solutions. To learn more, give us a call at (973) 882-4644.